GET UP TO SPEED ON ALL THINGS CYBER
We facilitate the exchange of crowdsourced cyber insights, experiences and differing opinions that challenge the status quo.
Our mission is to elevate cybersecurity awareness and defense through the content we generate. All of our original content is steered by our Content Advisory Committee, comprised of cyber leaders that you recognize and trust.
Our audience is diverse, ranging from CXO and board members, to members of the public with an interest in IT security such as students and business owners. Discussions address topics in business and personal security. Content published on Cyber Business Review is always ungated and freely available.
LATEST CYBER NEWS
02/02/2024 U.S. government sanctions Iranian officials over Pennsylvania water facility hack
The Iranian attack targeted a device manufactured by an Israeli company. (read more)
- - - - - - - - - - - - - - - - - - - - - -
01/29/2024 Wow! Mother of all breaches reveals 26 billion records: what we know so far
The supermassive leak contains data from numerous previous breaches, comprising an astounding 12 terabytes of information, spanning over a mind-boggling 26 billion records. (read more)
- - - - - - - - - - - - - - - - - - - - - -
01/22/2024 Smartphone ambient light sensors allow spying
Android and iPhone ambient light sensors can be turned into cameras, allowing malicious actors to secretly film unsuspecting victims and their surroundings. (read more)

Navigating the Digital Battlefield: The State of Cybersecurity in 2024
20-February
As we step further into the digital age, the importance of cybersecurity has never been more pronounced. In 2024, our reliance on interconnected systems, smart devices, and cloud technologies has reached unprecedented levels, making the protection of sensitive information and digital assets a critical priority.

Potential Solutions at the Right End of the Cyber Talent Pipeline
19-May | Written by Edward Pereira
For years we have been told that there is a severe shortage of workers with cybersecurity skills and experience, both in Canada and internationally. Most studies have described a crisis in terms of hundreds of thousands, even millions of job vacancies, depending on the scope of the study.

Twitch, Breached. A Hacktivism Reboot?
14-February | Written by Jean Loup P. G. Le Roux
A few weeks ago, the whole world reeled on the news that Twitch had been hacked. Millions of people instantly flocked to haveibeenpwned.com to see if their emails had been compromised and quickly changed their passwords.

IoT Security: New US Regulation to the Rescue!
5-March | Written by Jean Loup P. G. Le Roux
The many security problems linked to the Internet of Things (IoT) is not a new subject - cybersecurity experts have been warning everyone about these vulnerabilities for a long time now. While manufacturers have refused to heed these warnings (for the most part), legislation is now finally catching up.

When cloud software providers claim their solution is secure, watch for these 9 red flags
11 - January | Written by Eric Gold
There are serious consequences for both organizations and their stakeholders when software providers make misleading or confusing security claims. The livelihoods of businesses and individuals rest on such claims.

Cybersecurity Attacks in 2020: How Bad Did It Get?
23-November | Written by Jean Loup P. G. Le Roux
As we wrap up 2020, it's time to reflect back on this pivotal year that was from a cybersecurity perspective. Jean Loup P.G. LeRoux, CEO of I&I Strategy, shares his insights on cyber-related highlights and lowlights. He also offers some personal suggestions on how companies can ramp up their cyber posture as we head into 2021. – Steve Tso

Quantum Computing, Cryptography, and Information Security: Where Are We Headed?
2-November | Written by Luigi Bruno
Quantum computing brings next-level of computing power to cybersecurity to both the hacker and the defender. What exactly is quantum computing as it pertains to cyber? How does it change the game? What's its future? Luigi Bruno (Doctoral Candidate – McGill University, Faculty of Law) breaks it down in this CBR article. – Steve Tso

What the Twitter Hack Proves About Private Communications (Not Another Bitcoin Article)
1-October | Written by Jean Loup P. G. Le Roux
Back in July 2020, Twitter announced that 130 accounts had been hacked. The hackers tweeted from 45 of them from, 36 had their direct messages accessed, and 7 accounts had their data downloaded. How does a company as large and as sophisticated as Twitter get hacked? Jean Loup Le Roux takes a deep dive into what happened, and discusses ways for future prevention. – Steve Tso

How National Standards are Shaping the Digital Economy
25-August | Written by Matthew MacNeil
Standards are industry guardrails. Their purpose is to protect stakeholders. Ever wonder how standards are established in the technology space and how they affect our digital economy? This article by Matthew MacNeil (Director, Standards and Technology, CIO Strategy Council) explains the internal processes involved in creating the National Standards of Canada, and how they shape our day to day. – Steve Tso

Canada’s new Cyber Security Program for SMOs: An inside look at the development of Canada’s National Cyber Security Standard
18-August | Written by Matthew MacNeil
Hackers don’t care if you’re a Fortune 500 company or if you’re a mom and pop retail business. The notion of “we’re too small to get hit” is naive and dangerous in today’s age of automated cyber attacks. The CIO Strategy Council is working with the Canadian Federal Government to put forth a set of standards specifically catered for small and medium sized businesses. In this article, Matt MacNeil (Director, Standards and Technology, CIO Strategy Council) shares background on this relationship and provides a preview of what the standards may look like. – Steve Tso
Privacy in the Age of Facial Recognition
8-July | Written by Alexander Rau
If you have a social media account, someone already has a digital file of your face on their database. This is a privacy concern. Unfortunately for most users, the extent of this concern remains unknown, largely due to lengthy fine prints or tedious communication processes. This article by Alexander Rau journals his personal experience of approaching one facial recognition software company to find out exactly what biometric information they owned on him. It includes the necessary links in case you’re interested to run the same experiment. – Steve Tso
![How can someone legally access your data in the cloud [without you knowing]?](https://images.squarespace-cdn.com/content/v1/5e8fc3563a7ed3315515af04/1593817570368-8Q3D4N096ITA3QXI9PAG/How+can+someone+legally+access+your+data+in+the+cloud+without+you+knowing+-+Blog+Thumbnail+4%3A3+%28White%29.jpg)
How can someone legally access your data in the cloud [without you knowing]?
2-July | Written by Jean Loup P. G. Le Roux
Whenever the topic of unauthorized cloud data access surfaces, most point to cyberattacks as the expected culprit. Yet, there are LEGAL avenues for organizations to access your cloud data. Jean Loup P. G. Le Roux takes a look at two possible ways this can be done- through “jurisdiction” and “regulatory” systems and outlines what you can do to protect yourself against this. - Steve Tso
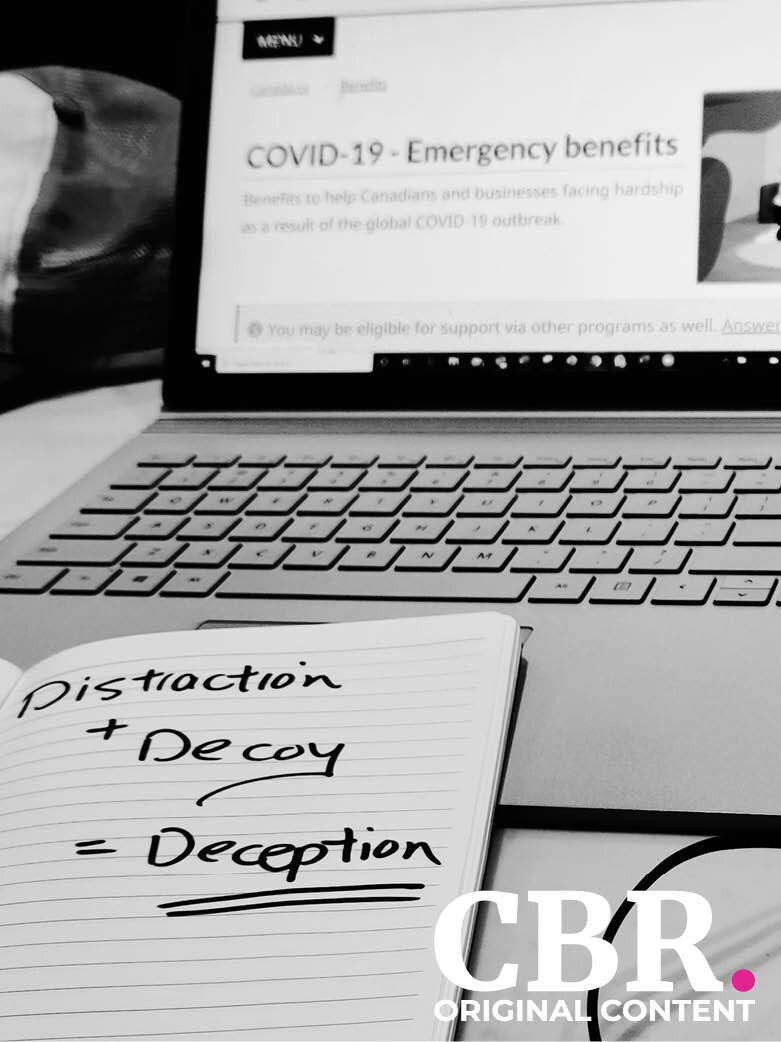
Deception = Distraction + Decoy
29-May | Written by Steve Tso
Phishing is a form of deception, and deceptions are comprised of two components: a distraction, and a decoy. The greater the distraction, the more effective the decoy. Both work together to entice its victims to commit. CV-19 represents an impactful distraction that’s prolonged. And hackers are taking advantage by pairing CV-19 with a myriad of relatable decoys. This article discusses the ramification of this through the lens of a typical Canadian family.
Buckle Up! Because Cyber Saves Lives
11-May | Written by Steve Tso
Similar to not wearing a seat belt, not taking cybersecurity preventative measures is irresponsible. In this article, I draw a comparison between the two and explain how getting to the point of being numb with something that’s clearly in the wrong doesn’t make it right. I then discuss the origins of Cyber Business Review, how it works, and how you can get involved.

IT’s New Security Challenge in a Post-Pandemic World
11-May | via Forbes
There’s been much discussion around what the office of the future may look like post COVID-19. However, there hasn’t been much information on how this extends to healthcare facilities and how the ER of the future may operate…

Hacker Sells 22 Million Unacademy User Records
8-May | via Bleeping Computer
We’ve all heard it before, and some may even be numb to it. “Company X got hacked and Y amount of personal data was stolen”. Well, what does that really look like? This article from bleepingcomputer.com paints a dark reality on what hackers sell post breach…

SUBSCRIBE TO OUR NEWSLETTER
to receive news and updates
By signing up, you agree to our Privacy Policy.

